Sync uses links as a means of sharing folders. Once you receive a Link to a folder and click on it, you will be brought to a special landing page on the Resilio website. This page will contain some basic info about the folder you are about to receive (folder name and size).
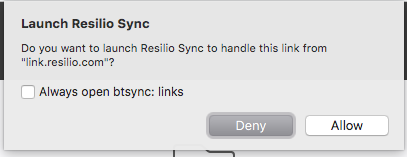
- If this is the first time you’ve used a Link, the page will offer to either install Sync 2.x or open the link in Sync, if you already have it. Your browser might also confirm whether you want to open btsync: links using Resilio Sync application.
- If you’ve opened Sync links in your browser before, the page will immediately transfer the link to Sync app. It means, Sync will automatically open and ask you where you want to save the folder.
Link structure
Sync links contain a minimum of information that Sync needs in order to start syncing. Here is a sample link:
https://link.resilio.com/#f=photo&sz=67E6&t=1&s=I6JBBZOB5OXCUV7WRIJDEXCZECGN4XZW&i=CAPXP6DZX5DLU7TD5L2NRXM4MDRNARNSN&e=1495791137&v=2.5
Let's see what each parameter means.
https://link.resilio.com/
The landing page on Resilio server. If the user confirms that Sync is installed, Resilio server simply replaces "https://" to "btsync://" so the link can be opened by Sync application.
f=SyncFolder
Name of the sync folder.
sz=25E7
Approximate size in exponential format.
s=Y5LHI6...
Folder ID in Base32 encoding.
i=CMASN3...
Temporary key, used to connect to the folder owner.
e=1426...
Link expiration time in Unix time format.
v=2.5
Version of Sync client which produced link
Note that parameters are separated from URL with the hash symbol "#" and are not actually sent to Resilio server.
Simplified link connection flow
Peer A is an owner of sync folder and shared the link. User A created an identity.
Peer B received the link and wants to sync the folder from Peer A. User B created an identity.
- On Peer B side, the link is opened and transferred to Sync app from the web-page or added to Sync manually.
- Peer B’s Sync uses the temporary key from the link to connect to Peer A and sends a request for folder access. This request also contains Peer B's locally generated public key.
- Peer A’s Sync receives the request and asks the user to approve it, showing Peer B's public key fingerprint and user name.
- By comparing the public key fingerprint, Peer A can make sure that Peer B has genuine identity before giving him/her access approval.
- After the approval is granted, Peer A generates an X509 certificate for User B and sends it to Peer B. This certificate will be used later to access files. There is no way for Peer B to get this certificate before all the steps above are successfully completed.
- Peer A adds User B's identity to Access Control List and signs it with his own certificate, granting User B access to the folder on a certain level (from "No access" to "Owner").
- Peer B gets the certificate and uses it to establish connection and access the folder contents.
After connection is established, the peers follow the standard flow of data synchronisation.